Today on the Twitter was discussion about Edge extensions which are controlled by Microsoft Intune.
Why not to use new feature to manage extensions? Available via Admin Center?
— Jakub Piesik | MVP @ Windows 365 (@dzejzipl) July 13, 2023
And this discussion is reason why I decided to write that post where I will be describing newest feature to manage Edge extensions via Admin Portal. This feature is currently in public preview – so still not in GA (General Availability) so some things can change later.
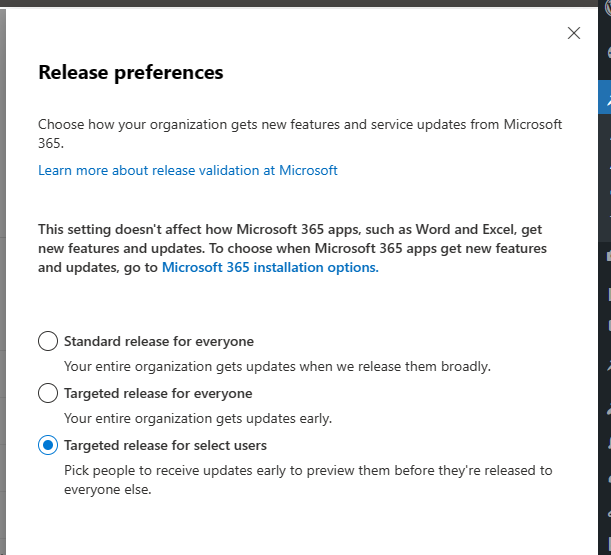
First, before this feature will be released to the GA – you need to to opt-in for all preview features for specific users / or whole organization. To do that, visit the Microsoft 365 Admin center > Settings > Organization profile > Release preferences.
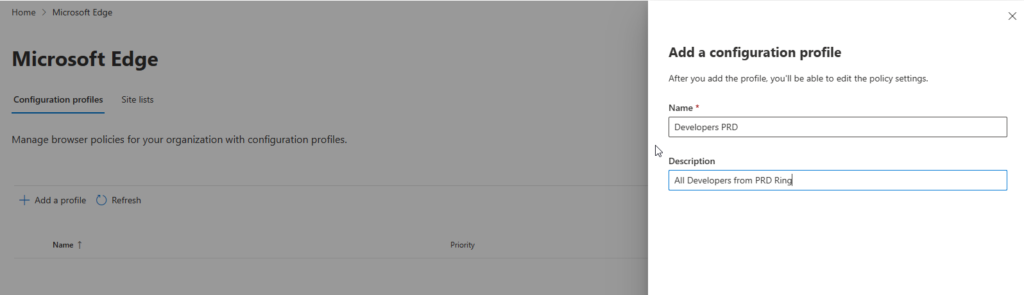
After that, you can wait some time and visit again Admin center > Settings > Microsoft Edge and select Configuration profiles.
On this page you can create specific configuration related to the extensions and polices and after assign to proper groups.
On my case, I will create some configuration profile for Developer roles.
Click on the Add a profile button and provide a name and description.
Now we can start with primary work – managing the polices and extensions.
First, we will focus on the:
Extensions
For example, we want to add Adblock extension from Google Web Store – yes, it is possible!
- Open configuration profile which you want to edit
- Go to the extensions > Select extension
- Now you can select from configurable Microsoft Edge extensions with providing name or Extension ID
- Or you can add external extension from Google Web Store
- I will focus now on the second method
- You need to find Extension ID from URL: https://chrome.google.com/webstore/detail/adblock-%E2%80%94-best-ad-blocker/gighmmpiobklfepjocnamgkkbiglidom?hl=pl. In my case it will be information which is marked with bold text.
- Next go to the External extensions and provide ID, name and description.
- I will also add standard Microsoft Edge extension – for example, something for JSON formatter.
After saving details, my extension tab will be looks like:
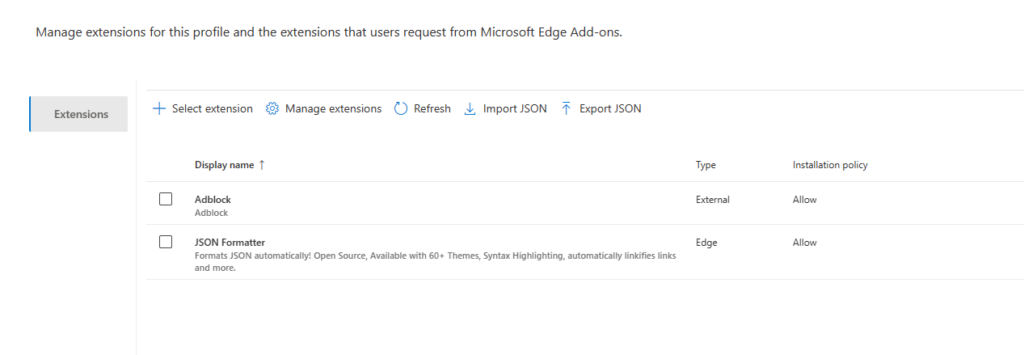
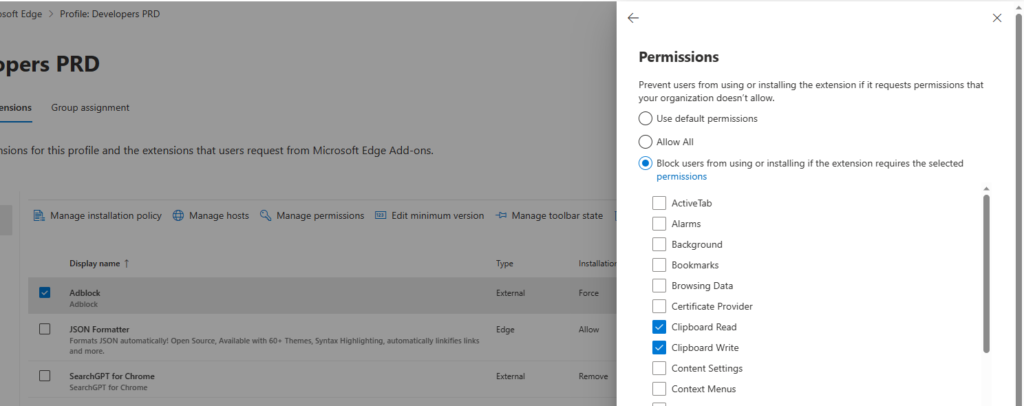
Now we can manage those extension and configure installation policy, hosts to which this extension have access, permissions and toolbar state. Amazing, right? Yep, I know…
For example, we will focus now on the Adblock.
If you click on the Manage installation policy you will be able what you can do with that extension:
- Allow – this setting will allow users to install it, or not if they don’t want to.
- Block – this setting will block users to install this extension. We can also select checkbox to uninstall this extensions from managed devices and add proper message to end-users when they want to install blocked extension.
- Force – this setting will automatically install extension on managed devices and end-users will be not able to remove it
- Normal – this setting will automatically install extension on managed devices, but end-users will be able to remove it
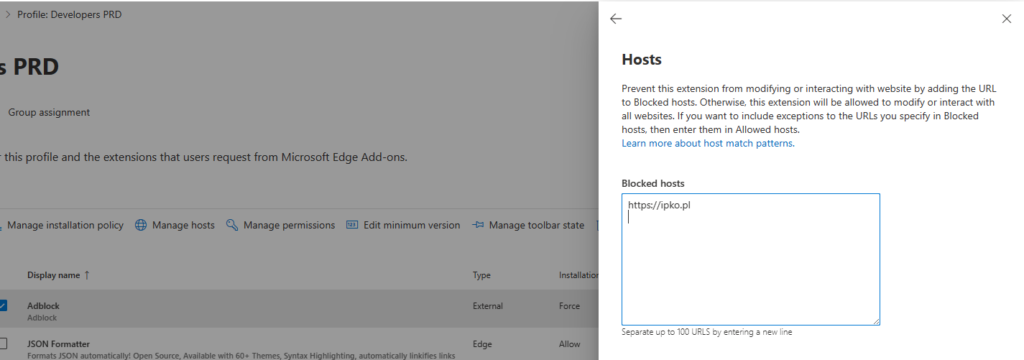
If you want to block extension to work on some websites, visit the Manage hosts tab.
You can also prevent installation of some extension which was already approved if newer version of extension require for example, usage of clipboard.
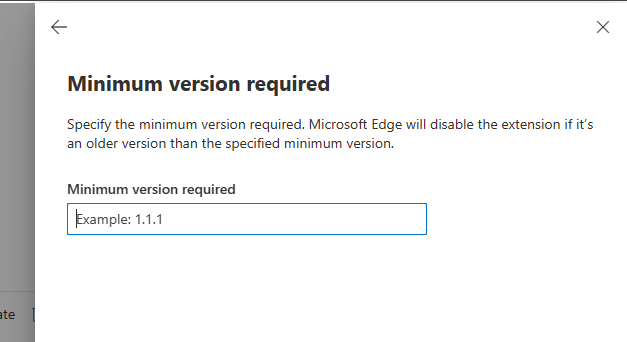
You can set up a minimum version for extension to prevent users to install older version.
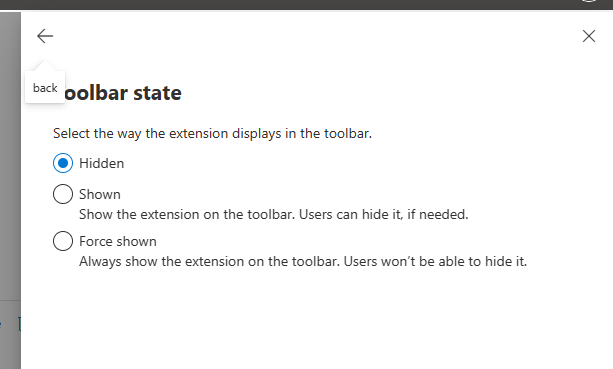
And the last option is – should this extension be visible for end-users or hidden?
As you can see, there are a lot option to configure for extension.
If you want to configure global setting, simple click on the Manage extensions button and you will see multiple settings which you can configure.
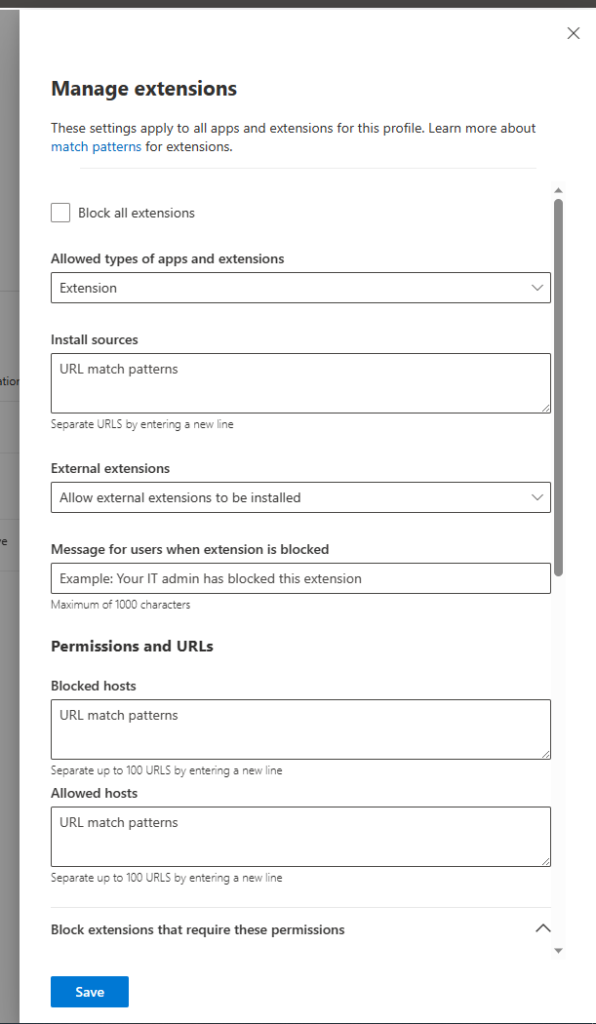
Configure them wisely and test first on the some IT users!
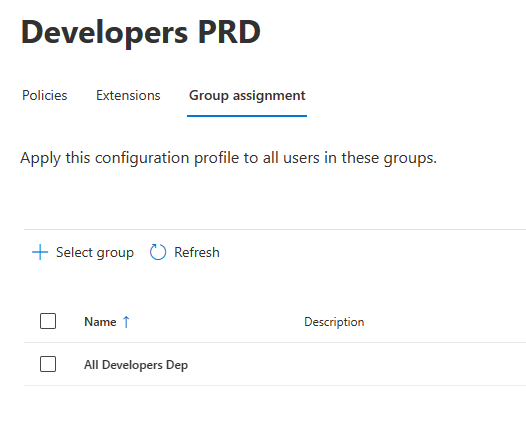
Assign profile to group
Step which is also required – and it is related to the group assignments. In my case, I’ve assigned policy to the All Developers
Do some registry changes! oO
Next thing until this functionality is on the public preview – are settings which are not in the Settings Catalog for Intune. We need to implement them by Intune engineers, in meantime we need to add two keys manually:
As wrote on this website please add two keys on path: HKLM\Software\Policies\Microsoft\Edge or HKCU\Software\Policies\Microsoft\Edge if you want to publish new management settings for current users only.
You need to add two new values DWORD with name: EdgeAdminCenterEnabled and second with: EdgeAdminCenterUseOCPSEndpoint. Both values should have data: 1 to enable those settings.
If you don’t want to manage those settings via Group assignment in Admin Portal, there is a second way to deploy:
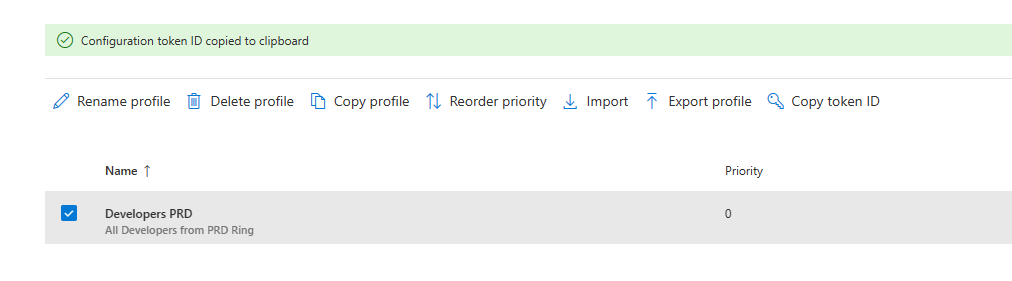
First, you need to have token ID. Just click on your policy and select Copy token ID
like on below screen:
Next, create registry one key on path: HKLM\Software\Policies\Microsoft\Edge or HKCU\Software\Policies\Microsoft\Edge if you want to publish new management setting for current users only.
Create new value with name: EdgeAdminCenterEnrollmentToken with REG_SZ type and data: Token ID copied from Admin Portal.
How it is looks from end-user perspective?
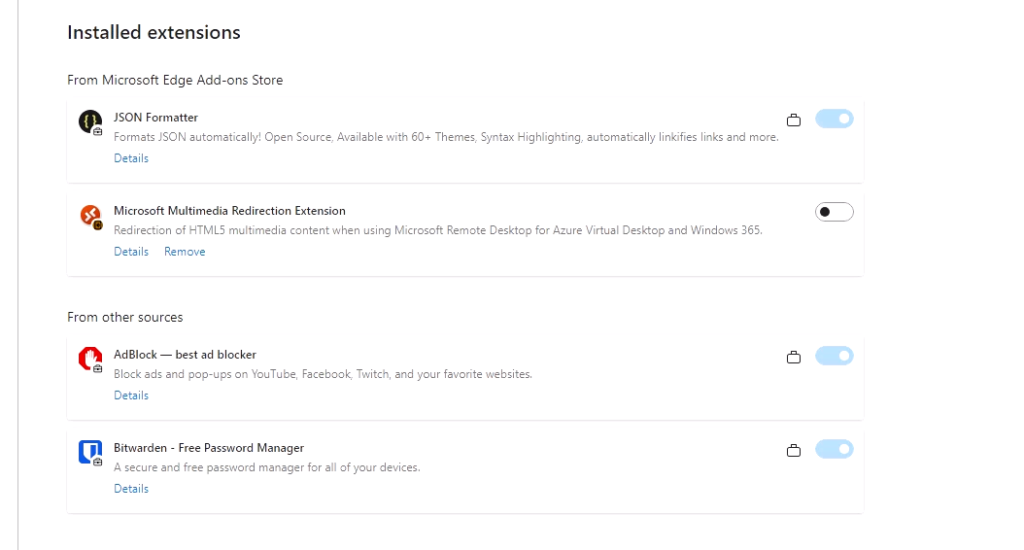
and the policies view:
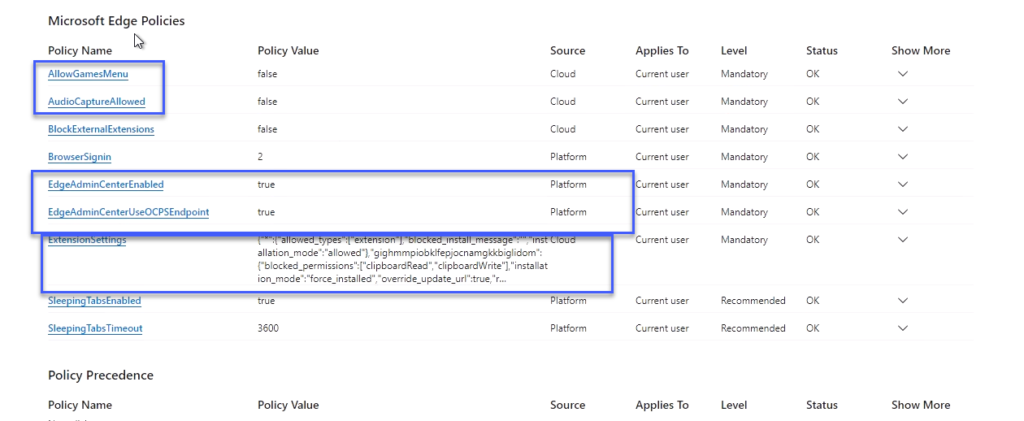
Additional polices?
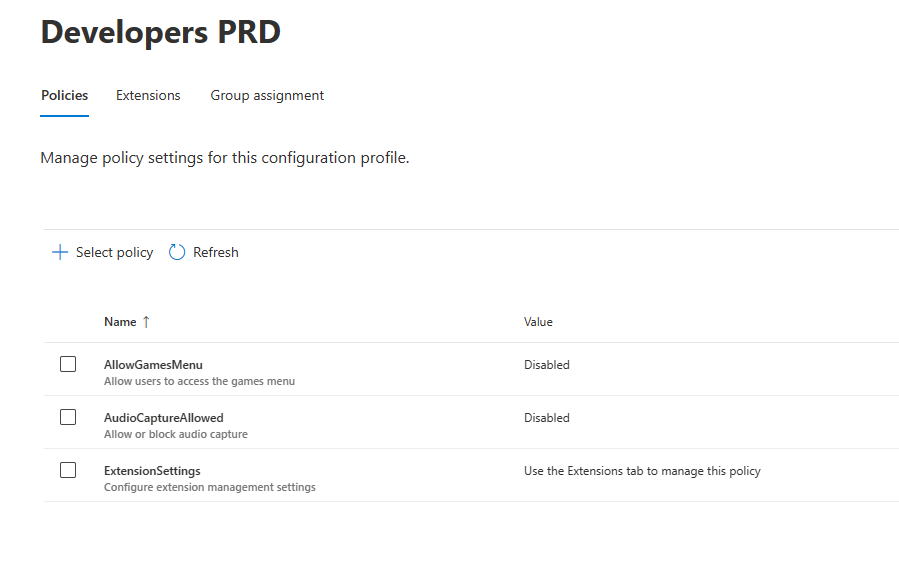
As you can see on my last screen, I configured two polices. Those settings can be configured on the Polices tab, like on my screen:
Additional information!
First deployment of newly created configuration profiles can take up to 24 hours on the end-user device.
But if you do some changes in existing profile, for example add additional policy – it can take up to 90 minutes to update settings on the end-user device.
You just need to be patient! 🙂
Also – one more information.
For example, you’re configuring that some extension don’t have access to specific website – like Adblock and below is my configuration:
"gighmmpiobklfepjocnamgkkbiglidom": {
"blocked_permissions": [
"clipboardRead",
"clipboardWrite"
],
"installation_mode": "force_installed",
"override_update_url": true,
"runtime_blocked_hosts": [
"https://ipko.pl",
"https://www.ipko.pl"
],From general understanding, – this extension shouldn’t be allowed on the specific website, but it is allowed. It is just not working on that website. I confirmed that with Microsoft.
Any questions? 🙂


